A key insight from ransomware prevention and recovery is this: Many incidents could have been prevented with simple and inexpensive measures. For cybercriminals, attacks are not a coincidence but a business model; time is money, and the focus is on “low-hanging fruit.” Conversely, eliminating externally visible vulnerabilities already significantly reduces the likelihood of an attack on an organization. In a sense, you fly “under the radar.”
Most External Attack Surface Monitoring (EASM) services, however, fall short - often certain areas are neglected. For example, during asset discovery, a remote access gateway of the backup data center may be overlooked, or cloud components may not be properly mapped, etc. - which can have fatal consequences. A single signal can be enough to put an organization on the attackers’ shortlist.
Many solutions generate overly long reports that have not been sufficiently validated and, with high “false-positive” rates, unnecessarily tie up internal resources. Through a human-expert-in-the-loop approach, the technical potential of the latest technologies including AI can be fully leveraged, while industry experts validate the results, contextualize them within the organization, and prioritize them accordingly.
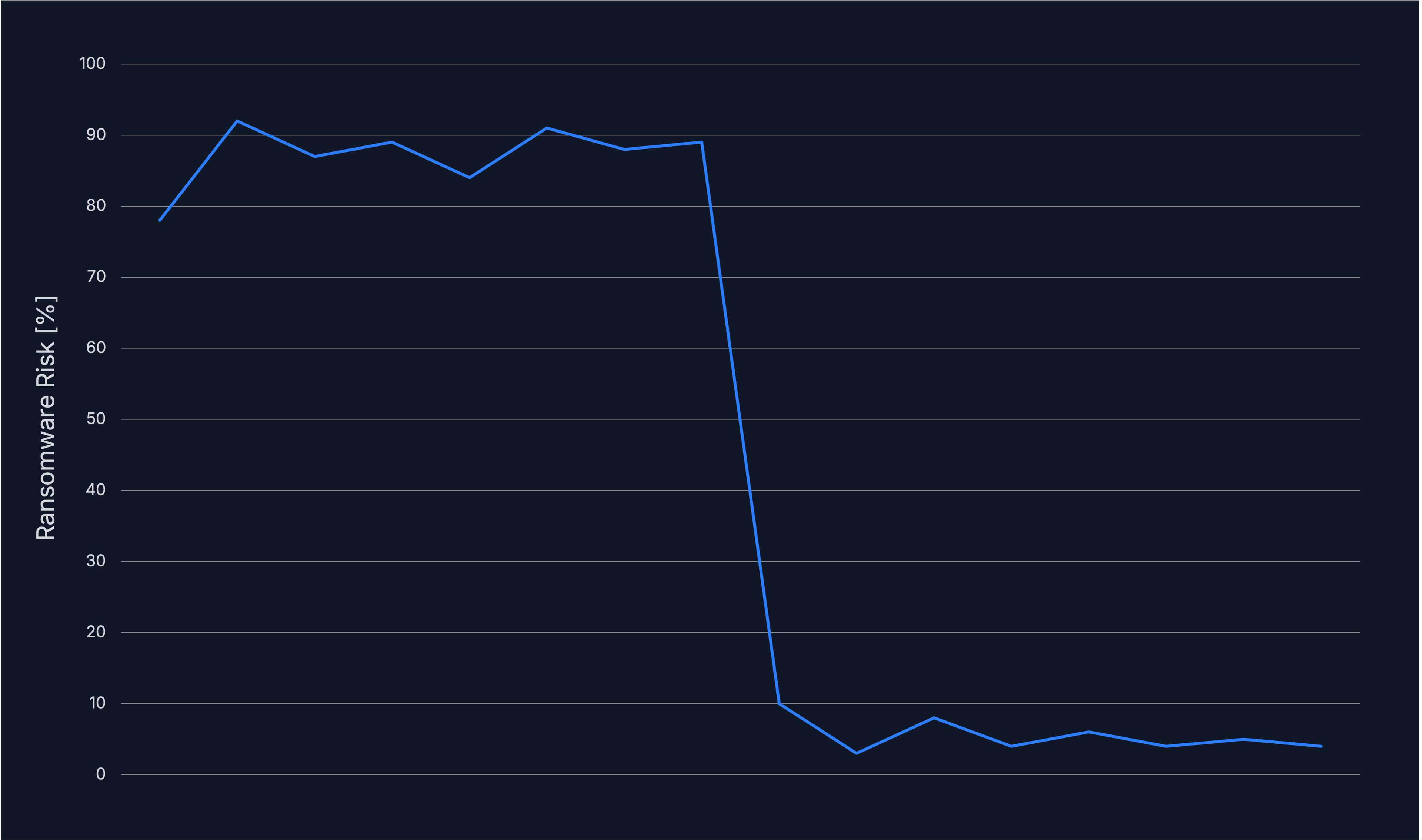
Cyway’s External Attack Surface Management (EASM) achieves an 85% reduction in ransomware risk with minimal effort on the customer side, using a specialized multi-layer approach:
Identification of the entire attack surface
Customers provide existing lists of domains/IPs — based on this, Cyway also detects related systems that may have been forgotten. With read-only access, coverage of cloud environments can be completed if necessary.
Interview
A short, focused interview is used to collect important additional key data and parameters, ensuring that the individual circumstances of the customer organization are properly understood.
Scanning
Systems are checked for vulnerabilities according to the latest findings. In addition to a wide range of technologies in the IT, OT, and cloud domains, dark web channels are also used to identify, for example, leaked credentials.
Validation & Context
Findings are validated by industry experts and assessed for relevance within the context of the customer organization. Concrete measures are prioritized based on return on investment.
Presentation & Tracking
Results are presented and discussed jointly by experts. Progress over time is recorded and made visible in a condensed form for management as well.
Your benefits
Professionalism with exceptional Return on Investment (ROI)
An established methodology ensures optimal effectiveness and is implemented by experienced cybersecurity specialists with extensive international practical experience in ransomware attack prevention.
Holistic – Effective
A single forgotten backdoor can lead to disaster. Cyway’s EASM therefore holistically reviews the relevant areas of your organization such as IT, OT, cloud, APIs, and the dark web for warning signals.
Meaningful, condensed report
There are no lengthy reports with theoretical vulnerabilities, as they cost a great deal of time and money on the customer side. All reports are expert-verified, with clear recommendations for action including quick wins; the most critical vulnerabilities first. Thanks to Cyway’s advanced risk analyses, measures are consistently prioritized according to the actual level of risk for your company. The reporting is ready for NIST CSF, ISO27k, NIS2, DORA, FINMA.
In reliable hands – with professional partners for emergencies
With the Cyway EASM service, you automatically receive direct access to our incident response and disaster recovery expert network. This ensures you do not lose time searching for the right support in an emergency.
Hesitation is not worth it
Do not wait for a security incident.
We are happy to be available to you for a non-binding consultation.